Sunday, 18 August 2019
US Leaves INF Because "Russia," But Points Missiles at China
August 9, 2019 (Gunnar Ulson – NEO) – We’re told that the US withdrawal from the Intermediate-Range Nuclear Forces (INF) Treaty singed in 1987 between the US and Soviet Union was based on claims that Russia had violated it.
While we continue waiting for Washington to provide evidence to prove these claims, the US itself admitted it had already long begun developing missiles that violated the treaty.
A February 2018 Defense One article titled, “Pentagon Confirms It’s Developing Nuclear Cruise Missile to Counter a Similar Russian One,” admitted that:
The U.S. military is developing a ground-launched, intermediate-range cruise missile to counter a similar Russian weapon whose deployment violates an arms-control treaty between Moscow and Washington, U.S. officials said Friday.
The officials acknowledged that the still-under-development American missile would, if deployed, also violate the Intermediate-Range Nuclear Forces Treaty.
Just as the US did when it unilaterally walked away from the 1972 Anti-Ballistic Missile Treaty in 2002, the goal is to blame Russia for otherwise indefensible and incremental provocations aimed at Moscow. For example, after the US walked away from the ABM Treaty in 2002, the US began deploying anti-missile systems across Europe.
But if Russia is the problem, why did the US also begin deploying similar missiles in Asia?
It is Washington’s goal of hemming in its competitors anywhere and everywhere that is at the heart of these serial treaty terminations, not any particular “violation” on Moscow’s part.
China Too
That the US already had missiles under development that would undoubtedly violate the INF Treaty before it accused Russia of such violations, is one indicator of Washington’s true intentions. Another is the fact Washington is rushing to encircle China with both defensive and offensive missile systems as well.
China is not a signatory of either the ABM Treaty or the INF Treaty. Its missiles are deployed strictly within its mainland territory with no plans by Beijing to deploy them anywhere else in the future.
The only threat they pose is to any nation that decides to wage war on China, in or around Chinese territory.
Washington’s behavior post-INF Treaty indicates that it was its intent to violate the treaty all along, creating the same precarious security crisis in Asia the treaty sought to prevent in Europe.
The New York Times in its article, “U.S. Ends Cold War Missile Treaty, With Aim of Countering China,” would explain:
The United States on Friday terminated a major treaty of the Cold War, the Intermediate Nuclear Forces agreement, and it is already planning to start testing a new class of missiles later this summer.
But the new missiles are unlikely to be deployed to counter the treaty’s other nuclear power, Russia, which the United States has said for years was in violation of the accord. Instead, the first deployments are likely to be intended to counter China, which has amassed an imposing missile arsenal and is now seen as a much more formidable long-term strategic rival than Russia.
The moves by Washington have elicited concern that the United States may be on the precipice of a new arms race, especially because the one major remaining arms control treaty with Russia, a far larger one called New START, appears on life support, unlikely to be renewed when it expires in less than two years.
Here, the NYT admits that despite Washington claiming its termination of the INF Treaty was prompted by Moscow, its own actions since indicate Washington was already well underway of violating it itself. It did so not only to threaten Russia, but also to threaten China.
After months of accusing Russia of undermining the INF Treaty, the NYT itself reveals it was Washington who solely benefited from it, and specifically in terms of targeting China:
…the administration has argued that China is one reason Mr. Trump decided to exit the I.N.F. treaty. Most experts now assess that China has the most advanced conventional missile arsenal in the world, based throughout the mainland. When the treaty went into effect in 1987, China’s missile fleet was judged so rudimentary that it was not even a consideration.
The prospects of the US signing a new treaty with either Russia or China (or both) are nonexistent. The NYT article also reported that:
Chinese officials have also balked at any attempt to limit their missiles with a new treaty, arguing that the nuclear arsenals of the United States and Russia are much larger and deadlier.
The NYT fails to mention the other, and perhaps most important factor preventing Beijing from signing any treaty with Washington; Washington has already demonstrated categorically that it cannot be trusted. It just walked away from the INF Treaty based on deliberate lies implicating Russia while Washington all along was developing missiles it planned to deploy around the globe to hem in both Russia and China.
Dangerous Desperation
While the Cold War is remembered as a precarious time, it was a time when agreements like the ABM and INF treaties were not only possible, they were signed and for the most part adhered to by two global powers who could agree an uneasy balance of global power was preferable to large scale war (nuclear or not) between the two.
While the Cold War is remembered as a precarious time, it was a time when agreements like the ABM and INF treaties were not only possible, they were signed and for the most part adhered to by two global powers who could agree an uneasy balance of global power was preferable to large scale war (nuclear or not) between the two.
During the Cold War, Washington was confident that it could not only maintain that balance of power, but eventually tip it in its favor, resulting in global hegemony. The collapse of the Soviet Union and the US invasion of Iraq certainly seemed to prove those behind this mindset right. But the window was already closing on the establishment of an uncontested US-led international order.
Today, Russia, China and a number of other emerging regional and global powers have all but assured US hegemony is no longer a viable geopolitical objective. The confidence that allowed the US to sign previous treaties and uphold them along with their Soviet counterparts no longer exists.
We live in a world today where the US has become a tremendous danger to global peace and security. The inability of treaties to exist that were even possible during the tense days of the Cold War takes us into unprecedented and dangerous territory.
Only time will tell if both Moscow and Beijing can find other mechanisms to avoid a dangerous and wasteful arms race in their backyards as a stubborn United States not only refuses to leave, but insists on bringing in incredibly dangerous weapons that will wreck havoc not on the territorial United States, but on the nations of Europe and East Asia should Washington’s desperation progress even further amid its wanning global power.
Gunnar Ulson, a New York-based geopolitical analyst and writer especially for the online magazine “New Eastern Outlook”.
River to Sea
 Uprooted Palestinian
Uprooted Palestinian
The views expressed in this article are the sole responsibility of the author and do not necessarily reflect those of the Blog!
Sayyed Nasrallah on “Grand Victory Day”: Any Future War Will Witness Live Streaming of Destroying ‘Israel’
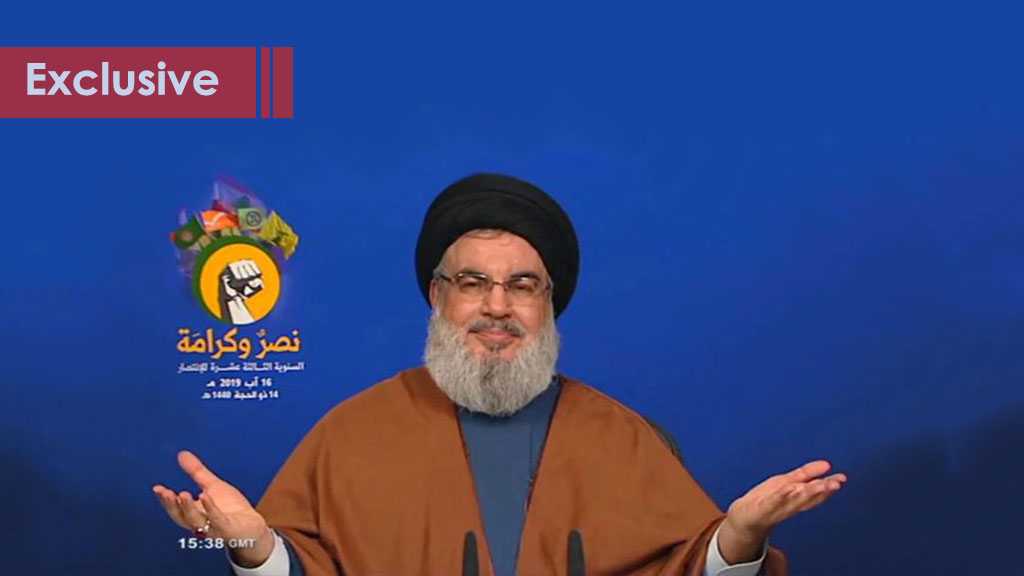
Beirut – Hezbollah Secretary General His Eminence Sayyed Hassan Nasrallah delivered a televised speech during the Lebanese resistance party’s celebration of the 13th anniversary of the “Grand Victory” during the ‘Israeli’ 33-day July 2006 war on Lebanon.
Sayyed Nasrallah stressed that “The resistance took advantage of the July 2006 war experience, setting a developed military system to defend our land.”
He further noted that ‘Israel’ has been trying over 13 years to renovate its ground forces and its confidence to achieve victory but it is still disable to do that.
Voicing the strength of the axis of resistance, His Eminence stressed that the Zionists wanted during the July war to put an end to all the states of resistance in the region, however, he stated “today we have an axis of resistance that stretches from Palestine to Lebanon, Syria, Iraq, Iran and Yemen.”
Sayyed Nasrallah reiterated an earlier promise that the enemy’s brigades and their tanks will be destroyed live on TV screens, adding that the world will witness the live broadcast of the destroying the ‘Israeli brigades that would enter Lebanon.”
His Eminence further explained that “The former head of the strategic planning at the ‘Israeli’ army confessed that the enemy’s entity is small and breakable, and that with a few number of accurate missiles, Hezbollah is able to inflict heavy costs on it in any war.”
Sayyed Nasrallah further highlighted the ‘Israeli’ domestic front’s chief’s saying that the “the borders between the domestic civil front and the military one will disappear in the first phases of any future war with Hezbollah.”
Resistance’s cost way less expensive than submission
Hezbollah Secretary General stressed that “We can now rely on the power of the axis of resistance which we boast belonging to,” noting that the martyrs of the stabbing operation that took place on Thursday in al-Quds are the sample of the Palestinian generation, the generation of the future and the resistance.”
Tackling the issue of resistance in Syria, Iraq and Yemen, His Eminence said “Syria endured the universal war and is heading with stable steps towards victory,” adding that “a strong and faithful resistance in Iraq forced the Americans to withdraw.” He then went on to say the “Yemen today is in a state of legendary endurance and stability, and that there are signs of the near defeat of the aggression.”
The resistance leader considered that “relying on the axis of resistance leads to stopping the aggression against Yemen thanks to the endurance, and will prevent Iraq from returning to the American hegemony.”
“With the might of the resistance front, al-Quds and the sanctities may be restores, and Gaza remains dignified with the hope filling the hearts of the Palestinians.”
His Eminence noted that “the cost of resistance is way less than that of submitting and compromising,” stressing that with the resistance the land, dignity, oil, sovereignty and honor remain, while with submission they would take them all.
Regarding the axis of resistance, Sayyed Nasrallah said that “when talking about a US war on Iran, the axis of resistance is the one that prevents the war through its solid stance, endurance and readiness to burst the region out.”
What prevents a war is the cohesion of the resistance front, Sayyed Nasrallah added.
Naming those pushing the region towards a war, Hezbollah Secretary General listed ‘Israeli’ Prime Minister Benjamin Netanyahu, Saudi Arabia, the United Arab Emirates and some Gulf countries: “We want to stop the wars in Yemen and Syria and preserve stability in Iraq and Lebanon.”
Hinting to US President Donald Trump’s retreat from waging a war on Iran, Sayyed Nasrallah explained that it is because Trump recognized how strong and capable Iran is on the military level, not to mention its courage and bravery.
Resistance didn’t spare Zionists from fleeing under fire
Regarding the square of confrontation (comprising the villages of Ainatha, Bint Jbeil, Maroun al-Ras and Aitaroun) where the celebration was held, Sayyed Nasrallah said this place witnessed one of the major battles during the July war, and it was a main decisive point during the war.
“The enemy was eyeing Bint Jbeil because it would have represented a moral and military achievement upon which it would build its achievements during the rest of the war,” the resistance leader explained, adding that “the Zionist war minister insisted on Bint Jbeil where the 200 Liberation celebration was held to deliver a speech in which he tells the world that ‘Israeli’ is not feebler than a spider web, but he also failed.”
Sayyed Nasrallah noted that “the resistance fighters confronted the enemy’s army a few meters away from one house to another and under tough military circumstances, and Allah blessed them with victory.”
The resistance didn’t spare the ‘Israeli’ from fleeing under, Sayyed Nasrallah said, explaining why the enemy committed massacres in the villages. “The ‘Israeli’ army wanted to present a field achievement but its defeat in Bint Jbeil made it desperate from making any ground achievement.”
Sayyed Nasrallah further praised the resistance men and the villagers who confirmed the spider web belief which the ‘Israeli’ was dying to eliminate.
Fire intended for the region will burn their faces
“The evidence on Iran’s power and will is the legal downing the US spy drone and the detaining of the British oil tanker,” Sayyed Nasrallah explained.
He further stressed that “The Iranian people refuse that their officials negotiate under pressure because their dignity is above all,” noting that “a war on Iran is a war on the entire axis of resistance, which means that the region will burn.”
Hence, His Eminence stressed that “the fire some are attempting to ignite in the region will burn their faces and entities, not only their fingers.”
The tripartite equation saved Lebanon
“Neither the US nor the international community and the Arab protection can remind Lebanon of a favor regarding its stability and freedom,” His Eminence said, adding that the tripartite equation of the Army, people and resistance is the one that made safety and stability in Lebanon.
“The scheme of 2006 war on Lebanon was supposed to crush the resistance in Lebanon and Palestine, crush the regime of Syrian President Bashar al-Assad, stabilize the US occupation of Iraq, eliminate resistance there, in addition to isolating Iran on the way to topple it,” Sayyed Nasrallah stressed.
“July war stopped for one reason which is that the US and ‘Israel’ recognized their failure in making any achievement in this war and their fear of things turning against them.
“Had ‘Israel’ continued the war after what it had faced over its course, it would have been heading towards a major catastrophe; and had the US scheme succeeded, it would have led to American hegemony in the region, and the starting point would have been the July 2006 war.”
Invitation to the Second Liberation celebration
Related Videos
Related Articles
- Lebanese President: Lebanon Will Emerge Victorious Again In Case of Any ‘Israeli’ War
- Iran National Security & Foreign Policy Commission Spox to Al-Ahed: Hezbollah Humiliated «Israel»
- That’s How #Hezbollah Navy Struck #Israel’s Warship SAAR-5 in 2006 War: Video
- Hezbollah Soldier Narrates How He Struck Israel’s Super Devora Boat during 2006 War: Video
- Sayyed Nasrallah’s “Beyond, Beyond Haifa” in 2006 Indicated Fall of the House of ‘Israel’: Video
River to Sea
 Uprooted Palestinian
Uprooted Palestinian
The views expressed in this article are the sole responsibility of the author and do not necessarily reflect those of the Blog!
Labels:
Axis of Resistance,
Deal of the Century,
Gaza,
Hezbollah,
Iran,
July war,
Lebanon,
Nasrallah,
Saudia,
Syria,
The axis of defeated,
UAE,
USA,
War on Iran,
Yemen,
Zionist entity
The Terrorists Among US- Cyber War and Privateers are the true Domestic Terrorists
August 14, 2019

What are Cyber Privateers and should you be afraid of them? Cyber privateers and cyber bounty hunters are criminals that are not covered under international law as government agents. In reality, this almost nullifies the chance for war to start over any particular hacking or compromised data event.
The problems hired or volunteer contractors create include a projectable legal attribution. You don’t have to be able to prove a country was behind a cyber attack or hack as long as you meet certain conditions. You can literally project the blame entirely to a different entity. The legal aspects will be covered in the next article.
It also nullifies the myth cyber privateers/ bounty hunters can use government tools on civilian or otherwise protected classes of people and infrastructure at will. International law doesn’t give people hired or volunteering to commit crimes under any auspices a free pass.
This is a new class of terrorism which separates a cowardly criminal element from the victim the same way a remotely detonated explosive would when used at a shopping mall. This criminal activity is spreading at a rate that raises alarm bells especially with the projection of 3 million untrained new hires over the next few years.
In the last article, I introduced you to Jimmy and Gary. After three difficult months of online Youtube training, both of our heroes were ready to take on careers as international men of mystery.
The absolute risk this presents to international peace and security should be obvious regardless of what accepted policy is. Everybody gets to spy or nobody gets to spy is the mantra this generation of Intel managers was brought along with. Most of the tools in the NSA arsenal have their start or at the very least a counterpart that is freeware.
Disgruntled people have access to software that can literally trigger a heart attack for someone with a pacemaker, cause a seizure, or even take control of your car.
More than 70 percent of the Pentagon’s Counterintelligence Field Activity: CIFA is staffed by green badge contractors. The majority of personnel at the DIA, the CIA National Clandestine Service, the National Counter Terrorism Center, and more than 80% of the NSA budget goes to private contractors.
All of the agencies are filled with what amounts to day labor. How many of them already have the keys to the barn that potentially starts the 4 Horsemen of the Apocalypse on their way?
State sized tools give emotionally inadequate and politically repulsive people the ability to illegally mimic or ply actions that are inherently governmental in nature. These same disgruntled overpaid groups fill out the do not fly lists. They are putting people on domestic terrorist watch lists. They are deplatforming journalists and people expressing opinions contrary to their employers and taking over social media and opinion for their employers.
The same groups are hacking websites and stealing financial account information. They gain access to bank accounts through phishing exploits and siphon your account dry. One group I am writing about did this to a family member of mine because of the exposure I’m giving. I’ll get back to that later in the series.
Over the last five years, I’ve not only described the role cyber privateers are playing in world affairs, but have been documenting the players and the damage they are causing.
This article will describe the now accepted US cyber policies that were written by cybercriminals to give themselves cover so they can use the American people and people of the world as their own personal cash cow or reservoir. If they don’t like you, no need to wonder who gets to pay for that.
The inherent problem with cyber privateers is covered in the job description as well as their rather fanciful notion they are anything but criminals.
Privateers operate as sanctioned pirates. These throwbacks pretend to operate like their 18th century inspirations did. Back in the day, the sponsor country allowed them to make money attacking merchant and military vessels they didn’t like but didn’t necessarily want a war with. When mistakes were made, privateers supposedly made reparations to the groups they victimized. They had to identify themselves and offer a remedy for damages.
The 2019 cyber privateer or bounty hunter is under no such compunction. They don’t identify themselves and their victims rarely know who hit them. In fact, when they do identify themselves, it’s just to gloat. They do it in a setting that implies the message that needs to get across without confessions that would hold up in a court.
If this sounds wordy, cutesy, or alarmist, private contractors have interrupted the power grid in Venezuela and hacked into Iran’s nuclear infrastructure. They are penetrating the power grid in Russia. This is an ongoing problem that’s exasperated by the fact legislators rely on the terrorists to draft the laws to protect them from everyone else.
Think of it this way, if Joey, going by the cool hacker name HedCh33z3, decides he doesn’t like Latvia, can he disrupt their electrical infrastructure, medical infrastructure, or elections?
The fact is they move in and out of government service so often, they never bother to switch hats or status. Think of it this way, Joey works for the NSA for a week under a subcontractor and picks up a ton of tools to stalk his Ex and sadistically destroy her life piece by piece. This is what happens when people assume the right to government powers without the authority or responsibility to use them.
Are you willing to send your kid to war or go yourself because Joey HedCh33z3’s ex-girlfriend’s family thinks he’s a creep and they are from XXX country? Yet, we are now snugly very close to being put in this horrific position by politically and emotionally stunted people.
Privateers are Terrorists
So, where do they get the right to do this? Starting right after September 11, 2001, OSINT and cyber started as a serious money-making cottage industry. In the last article, we closed with the DOD actively hiring cyber Bounty Hunters to hack into foreign countries infrastructure.
This practice didn’t just start yesterday. Since 2001, there have been many attempts to codify US hiring of cyber privateers or bounty hunters into law. What this has done is enshrine it in US cyber-policy. The DOD use of subcontractors says a lot.
- What are cyber bounty hunters and cyber privateers and what do they actually do?
- Work with direct action military subcontractors
- Work for NGOs, corporations, lobby groups
- Work for US government agencies like the FBI, CIA, DIA, DOD, DNI
- Work for political parties and causes
- Work for foreign governments like Ukraine as shown in this series against the interests of the American people
- Work for themselves
They provide Intel through OSINT and hacking. They provide direct action through hacking and Information Operations. Today, they are taking on inherently governmental responsibilities and making decisions they don’t have the authority to make and they make decisions that belong to State agencies.
- Who is the enemy?
- Who is friendly (or are there really any friends out there)?
- Who is a danger and how?
- Why are they a danger?
- What is their motivation?
- What steps will the US need to take to stop them, turn them in a different direction, or make peace with them?
One attempt to legalize this activity is called the Morgan Doctrine.
You’re aware that the U.S. Secretary of State is actually dumb enough to host her own email server. Even if you’re a third-world country without the infrastructure to create serious cyber attacks yourself, a few thousand dollars in Bitcoins to Hackers-R-US will get you zero-day exploits to crack just about any individual server. Either way, you’re going to OWN that server before the next national holiday (pick your country, pick your holiday).
The Morgan Doctrine states simply that if you attack my computers (or my banking assets held in US-based computers), then under a certain set of well-defined conditions, a licensed and bonded “cyber privateer” may attack you in your home country and split the proceeds with the U.S. government…You raid our bank accounts, we raid yours. You make money from off-shore child pornography, we’re going to loot your bank accounts and, with some REALLY creative black hat operations, you will be taken off the grid worldwide to the extent that you’ll not even complete a cell phone conversation for the remainder of your miserable depraved life.- The Morgan Doctrine
Who decides what is right, legal, or legally binding? Is it right when someone who gets paid to find you and accuse you also makes his money from destroying your life and reputation, or directly by stealing money directly from you?
According to the Morgan doctrine blogger who does this kind of work for Oracle, Salesforce.com, BIGFIX, and other technology companies, the answer is a big yes.
The USA followed by Ukraine makes up the highest percentage of over 50,000 readers which reflects the numbers the Ukrainian Diaspora hired to create the illusion of Russian aggression in Ukraine and the 2016 election interference meme. This is a serious attempt to push legislators for legal cover for what is accepted at the policy level.
Let’s spell this out. If a cyber bounty hunter or cyber privateer say you work for Russia while they work against Russia, according to this, you picked your side in the war they get paid to fight. It doesn’t matter if you don’t know you’re in one.
When they work for NGOs, foreign governments, political parties, and companies, they are given cover. They found out along the way they are entitled to your bank account as part of their payment as well as the joy of ruining your life every way they can. It means no more than a video game to them.
In the private sector they now illegally, harass, stalk, and locate people with no legal justification. They are trying to facilitate renditions and executions. Let’s be clear, these are your neighbors doing this to your neighbors.
Aric Toler and Bellingcat helped set up the functionality of Ukraine’s hit for hire website Myrotvorets (peacemaker). The only goal of the site is to publish personal and contact information of anyone they consider standing against Ukrainian nationalism so they can be dealt with by private parties.

The above clipped from Christelle Neant’s article should be clear enough to understand on its own and she asks the right questions. Bellingcat’s work with privateer groups has included trying to leverage their collective expertise and locate and rendition me.
Almost every time I’ve been threatened by Ukraine, it’s an American collaborator making the threat for them. The linked article shows one such person who also designed Ukraine’s Information Policy. He also wrote the policy paper for the US government’s cyber policy.
The people that testify for the US Congress on cyber and OSINT are the same people doing these things. They are training and setting up groups in multiple countries and under different auspices.
More than one of them trained the full spectrum of alphabet agencies. CIA, NSA, DIA, FBI, DNI, DOD, and we can keep going across the board.
They were behind setting up the policy that guided the Tallinn Manual defining cyberwar and international law. We’ll be opening that up within a couple of articles.
As a testament of their cyber mojo, they spent the last few years collectively trying to locate someone who didn’t change locations often and used normal communications and social media. I publish articles in 5 or 6 publications regularly. I have 4 or 5 different social platform accounts.

They couldn’t figure out that I was where I said I was for the last 5 years. This spring I wrote a Victory Day article with local video and interviews. Even though I clearly showed my location, they still weren’t too sure.
The one thing you can say about them and their ally Bellingcat is they are consistent. Consistently wrong that is. In Ukraine, Bellingcat’s chief source of Intel is Ukrainian Intelligence. This includes the Ukrainian State hackers that contacted me after my sister was hacked. Journalism from the Donbass side of the contact line is a crime against Ukrainian sensibilities.
This group supplies Intel to NATO and individual EU countries and makes the rounds in Congress. Bellingcat’s work in Syria is chiefly supplied by the other side of Bellingcat’s Intel fabricators who also work for Ukraine.
We now have Americans working with foreign Intel stalking Americans and foreign citizens/ journalists for foreign countries they know will be tortured and killed. This clearly falls under terrorist activity.
One side of the group that works for Ukrainian Intel contacted me for the first time the day after the bank account was hacked and cleaned out using the hacker’s preferred method. What was the reason for the sudden communication? He wanted me to know how smart he really was.
Yet, these same so-called super spies claim to be able to find information about things people are actively trying to hide like weapons systems, motive. Most of the time they don’t speak the language of the country they claim to have expertise for. They decide guilt even though reality shows they aren’t able to actually do the job. Strange, isn’t it?
It was US policy to make them extra-legal but not illegal in the US after 9-11. Congress worked with these groups to write laws that refuse to criminalize what they do when it’s done on citizens. In fact, it no longer matters which side of the spectrum holds the reins, they feel empowered and will continue to do so until laws are written regulating their industry.
Over the last articles, I developed a slow-burn look into the world of the private spy. The idea that in less than 4 years the industry wants to hire 3 million unlicensed, unbonded, and untrained experts to work both government and corporate Intel and spy gigs should scare the hell out of you.
Can you give me a reason why the US which already collects and analyzes every piece of data on the internet needs so many more of what amounts to interns working with state sized software packages?
That’s 82 US citizens per new hire private sector OSINT agent. They have to literally spend 4 days on each person they investigate (82 per year including babies) just to get a full year’s worth of work because of the existing DNI, FBI, CIA, DIA, DOD OSINT agents have the rest of the world covered.
How serious is the information I’m providing? The EU Computer Emergency Response Team (CERT-EU) sent the articles to the EU institutions, agencies and bodies as well as outside governments and agencies. This means the EU has real concerns about the practice, laws, and policies allowing the practice because of the inherent damage so-called bit-players in private Intel and Information Operations (IO) can do at home and abroad not to mention diplomatically.

After you grasp the magnitude of the problem and begin unwinding the moving parts it can become manageable again through lawfare. Legal and societal protections you take for granted no matter where you live went out the window as soon as these practices became the norm.
Even from street level, people can make large sweeping changes to the world. Before you poo-poo, the idea, look at the CERT-EU screenshot again. I believe this can be done because I have already done it.
Towards the bottom of the article, we’ll get into the international policy for cyberwar and non-war situations. The same people that I’ve been writing about for the last 5 years exposing how they go after groups with protected status also wrote the policy for the US Government, all the agencies. While they didn’t write international policy directly, people they trained or work with closely did.
Four years ago, I exposed a flaw that exposes them to justice in the Tallinn Manual and threatened to pursue it. I did this because to win, I needed that gap closed. Tallinn is about applying the laws of war to cyber. It is something that otherwise would get no mention at all because it’s not considered a gap in any other context.
They closed that specific gap verbosely and gave me the opportunity to show how sordid this mess is. This also paves the way to provide a real resolution from private spies attacking civilians, social groups, political groups, journalists and other protected parties. Myrotvorets and Propornot should take note as should the other better and lesser-known companies and personalities.
No one has the right to use what they, themselves, rightfully label as Al Qaeda tactics on civilian populations, social activists, journalists, and other protected groups without assuming the legal definition of a terrorist, i.e. cyber terrorist.
Should lawfare (legal activism) fail to provide a remedy, the penalties for cyber assault (terrorism) and the right to a vigorous defense against perpetrators is what can make the laws change-FAST. Terrorism is terrorism is terrorism.
Once that fact is established anyone supporting them or hiring them in any way shape or form is guilty of material or direct support of terrorist activities against their own nation. Congressman, what say ye?
Law and policy makers fell in love with this power they never had before because it gives them the ability to shape policy they have no right to change for the sake of constituent and lobbyist cash and gift donations. They create loopholes in the cyber laws they write with the help of the companies and practitioners engaged in criminal behavior (under every other circumstance). Today, they hire the same criminals to help them with elections. Oppo-research, reputation management, Information Operations, and even projecting their (congressman’s private) own foreign policy agenda into the international arena.
Imagine Congress asking a cybercriminal what kind of regulation or oversight their industry needed? What if Congress then asked the same societal deviants to write the laws that define the limit to what is legal they would agree to. Real criminals decided what the laws protecting their victims should be. They decided what the penalties should be if they got caught.
The tradeoff is this same Congress that was never allowed access to Top Secret information unless they have security clearance on their committee can get the actionable Intel before it’s marked “secret” if it’s gathered through OSINT by a private contractor working for US Intel agencies. That loophole makes it ok for anybody to move information before it’s been vetted and resell it.
Imagine these same legislators hiring you because you’re the expert they trust and they knowingly wink at the crimes you’re committing against your own people. They haven’t updated labeling the new twist on criminal law yet, and they won’t because you don’t want them to. And hardly anyone is referencing the same crimes using older precedent as a reference for prosecution or lawsuits.
This creates huge gray zones in the law. Gray zones are areas of law where even though something is illegal, there is no law on the books against a specific method of a known crime. Stalking is the easiest example. If someone is stalking you, follows you, and threatens you, we can all agree a crime was committed.
So is stalking a crime? Not if you are an OSINT practitioner doing it online because there is no legal or regulatory system you have to justify yourself to.
The gray zone, in this case, exists in a couple of areas. The first is attribution or identifying the perpetrator. This isn’t a small thing. The person with the Twitter handle “little ice cream girl” could actually be Stan from Milwaukee who was hired to sway the vote for his candidate. You annoyed him. The state sized software package he inherited working for XXX contractor that was working for the CIA toppling Antarctica is going to come in handy wrecking your life as thoroughly as the preverbal bull in the china shop.
The second is time and distance. Money concerns aside, if you are stalked, harassed, or threatened from the other side of the country or globe, what local prosecutor can even get his head around this new dimension of law?
Last year when I was originally going to publish this series, I spoke to an attorney specializing in international law. He listened for a short time and told me to stop. He didn’t want to hear any more. It wasn’t because of a lack of proof. His reasoned that the substance of what I was saying would put him in a very dangerous position.
It wasn’t his first rodeo and he claimed the last time around, his own national government refused to give him any cover or come to his aid. In his words, his government views taking on private Intel contractors as akin to taking on the CIA directly. And they weren’t willing to do that.
This is the attitude most people and even Congress takes. You can’t beat the deep state. But, the deep state ISN’T sworn-in law enforcement or agency personnel anymore. The illegal hiring practices for almost 2 decades gave private sector (green badges) oversight of agency personnel and projects. The problem multiplies because they trained the managers at the agencies and wield tremendous influence.
A fundamental truth is private industry cannot take on inherently governmental responsibilities legally or successfully. In the end, a company’s only consideration is their bottom line. Patriotism and companies part ways when it is no longer profitable. That’s just business.
What Congress and policymakers have done is to allow a huge gray area to be created where criminals are allowed to thrive because they provide political candy in the form of mostly fake Intel that supports whatever project a member of Congress needs to appease his pet cause lobbyists.
This could all be cleaned up by applying existing stalking and assault laws to online stalkers by making the punishment extreme. The same goes for political activists that are doing this under the cover written for them. As long as they volunteer, they are not targetable for retribution internationally. If they are provably working with a country or company working with a country, as soon as they stop, they can’t be touched. How’s that for a policy?
Fixes for Online Troll Remediation
Putting all these online Intel related cottage industries under rigid government oversight and forcing them to document what they are doing and to whom both domestically and internationally is the one way any type of privateer scenario that is already OK’d by the current policy can actually work. It also gives protected classes the opportunity to stop harassment and demand damages. This is precisely why it won’t happen unless it is pushed hard.
Congress could write and pass a one-page bill to write protection against this if they had the inclination. The crimes exist in the law already. The only expansion is applying them to technology. They won’t.
The other more realistic approach is to demand US president Donald Trump takes out his magic pen and write an executive order guaranteeing reasonable protections and appropriate punishment.
This is unlikely to happen because the move would literally box in this already metastasized invasive cancer commonly called the deep state. The celebrated work of the CIA and FBI infiltrating perfectly legal civil groups or dispersing propaganda through news platforms like the New York Times has been rendered child’s play in both scope and impact.
And we’re still waiting to see what kind of trouble 3 or 4 million unregulated new hires will bring domestically and internationally.
International Law and Policy for Online and Cyberattacks
Next, let’s establish a few things directly from Tallinn Manual I. From a 2015 article I’ll be highlighting a lot more in the next article I showed clearly that:
- Civilians are a protected class.
- If you work with a foreign country against their perceived enemies you are considered a military asset even if you work for a private contractor. You are targetable in every sense that word conveys.
- If you work with a foreign country against their perceived enemies you are considered a military asset and attacks against civilians is a terrorist act.
- To my knowledge no western country allows its citizens to make war on each other or citizens of other countries they are at peace with. The Black Letter Rules include: Rule 23.3 Cyber attacks against civilians is a war crime defined by rule 32.
- Rule 26.7 The concept of “belonging to” defines whether you can be targeted or not. This rule defines civilians as off limits unless they are “engaged” in real war duties. It includes undeclared relationships where behavior makes it clear which side a person is fighting for.
- Rule 26.9 Virtual online communities and people expressing opinions do not qualify as combatants.
- Rule 30 defines a cyber attack as a non-kinetic attack reasonably expected to cause damage or death to persons resulting from the attack. If attacker mistakenly calls civilians lawful targets, the attack on civilians still occurred. It is a crime. This is an important consideration considering how interconnected the internet has made people.
- Rule 31 Psy-Ops including leaflets, mass emails is not prohibited behavior.
- Rule 33 If there is doubt to the status of a person, that person is to be considered a civilian and not targetable.
- Rule 35.5 Gathering information for the military makes you a combatant.
- Journalists are prohibited targets.
- Once an attack is made, the retribution is legal and does not necessarily need to be in kind.
A cyber attack can be met with conventional weapons.
- Rule 41 Means and Methods describes cyber weapons broadly as the means to carry out cyber war by use, or intended use of cyber “munitions” designed to cause damage, destruction, or death to its targets. The breadth of the rule is required because of the wide array of possible attacks through cyber means.
Now, the first loophole I wanted to be closed comes from an inverse look at a cyber war attack including stalking and targeting protected classes. Here’s how this can be elevated to war crimes.
Cyber can come from anywhere across the globe, anonymously, and stealthily (you may not even realize you were attacked). Because of today’s events people being attacked are from different parts of a given country and even spread across the globe.
This means if political or social activists are targeted, it may look like random events even though the numbers of victims could be in the hundreds of thousands or potentially millions. Here’s the two-minute example from one of the industry pioneers that attack civilians.
If the attack is considered as a single event because one single protected class or group is targeted even though they are physically at different geographical locations, we can reach the threshold for a cyber attack governed by the laws of war. Since it’s civilians, it would need to be litigated but the settlement would come from the offending country. Cha-ching!
Nevertheless, I collected a sample of 50+- IP addresses. Thank you, Mr. Justin, you are an eminently useful idiot.. . Also, many (most?) of the US readers were at work when they visited antiwar.com. Those US readers are concentrated in New York metro, Washington DC, greater Boston, the Bay Area, and Illinois (Chicago and main campus, U of I). Meanwhile, the Russian readers (there are only two in the dataset) are split between Moscow and Saint-Petersburg.”- Andrew Aaron Weisburd @webradius

I ask why is this Info war agent that trained all the US Intel agencies, NATO, and works for Ukraine geolocating American citizens for Ukrainian purposes?
This group is a political social group reading and commenting at a media platform in a country that still has the 1st Amendment. It is a protected class.
THIS IS ONLY ONE STEP FROM A WAR CRIME. As soon as it’s established Weisburd is doing this for less than Ukraine’s hit for hire site Myrotvorets, we are in the neighborhood of WAR CRIMES. Interestingly, Weisburd helped spawn Myrotvorets and enhanced Ukraine’s geolocation abilities.
Secondly, if it doesn’t meet the war threshold, it is still a terrorist attack on protected groups. When I proposed that injured parties have the right to robust self-defense, Tallinn II closed up the language by barring civilians the right of redress, self-defense, or preemptive assault because this was the domain of nations.
But, that language also makes it imperative for them to persuade Congress to step up to bat and write restrictive laws or the future looks very bleak for private industry spies and IO working against the public interest.
But, that language also makes it an imperative for them to persuade Congress to step up to bat and write restrictive laws or the future looks very bleak for private industry spies and IO working against the public interest.
Did Andy Weisburd take that final step? Stay tuned, it’s detailed in the next articles. Next up, we’ll show the same small groups of OISINT and IO trailblazers are responsible for most fake news, bad Intel, and are covering up crimes against humanity.
Make no doubt about it, they are terrorists. They can be treated like terrorists and people have the right to robustly defend themselves.
River to Sea
 Uprooted Palestinian
Uprooted Palestinian
The views expressed in this article are the sole responsibility of the author and do not necessarily reflect those of the Blog!
Why Continuity

by Eve Mykytyn
Marissa Brostoff and Noah Kulwin wrote an opinion piece about the Epstein scandal in the self-described leftist outlet Jewish Currents. Entitled “The Right Kind of Continuity,” the article is a ‘who is to blame’ piece. Is Epstein’s scandal peculiarly Jewish? If so, which Jews are to blame? Not surprisingly, their analysis finds a few very rich and generally right wing Jews guilty. First the authors point to the number of Jews seemingly involved with Epstein, even noting that Woody Allen was the first name in Epstein’s little Black Book. But they dismiss the significance of the disproportionate number of Jews friendly with Epstein, concluding that since “[a]fter all, Epstein’s friends also included plenty of prominent non-Jews (Donald Trump, for instance),” Jews were not particularly to blame.
Instead, the authors find that Epstein presents a ‘Jewish’ scandal because most of the men alleged to have financed his operation are Jewish. Epstein was not, as this article and many others describe him, a ‘financier,’ a term Oxford defines as “[a] person concerned in the management of large amounts of money on behalf of [others].” As of now it is unclear if and how much money Epstein was ever authorized to invest. Epstein was a taker of money, and was long tied to billionaire Leslie Wexner and with a number of other wealthy Jews including Leon Black of Apollo Global Management and Glenn Dubion of Highbridge Capital.
Why did these wealthy men finance Epstein? Most have speculated that Epstein ran an intelligence operation or that he was blackmailing his benefactors. The authors take a different approach. They point out that Wexner, along with other Jewish billionaires such as Adelson and Bronfman (neither of whom are connected to Epstein) , have given hundreds of millions of dollars to Jewish charities that fight assimilation. Apparently these men believe that ‘Jewish continuity’ is declining among American Jews as evidenced by statistics that “synagogue membership and affinity for Israel were in decline, interfaith marriage was up, and Jewish fertility rates were down.”
This claim is dubious, The Jerusalem Post recently noted that the rate of participation in Jewish Life by American Jews has been “remarkably stable”, and that the children of intermarried couples identify as Jews at the incredible rate of 80%.
But Steven M. Cohen, academic and demographer for Jewish charities, produced countless statistical reports of assimilation for wealthy donors emphasizing that “if they wanted American Jewish life to continue, they would have to prioritize the goals of “creating more Jewish marriages and filling more Jewish baby carriages.” (Cohen was himself dismissed from Hebrew Union College last year following accusations of serial sexual harassment.)
Reproduction, the article claims, both biological and social, is at the heart of ‘Jewish continuity’ programming.
In the weirdest story to emerge from the Epstein scandal, the New York Times wrote that Epstein was desperate to replicate himself and planned to use his New Mexico compound to fulfill his desire “to seed the human race with his DNA by impregnating [large numbers of] women…” The article claims Epstein’s desire for clones was different only in degree from the ‘Jewish continuity project, finding little difference between Epstein reproducing himself and the Jewish establishment that “poured millions of dollars into [reproducing] its own image.” After all, the authors ask, “Which is the greater narcissism?”
After finding the financial backers of ‘Jewish continuity’ guilty of self love, the authors present an extraordinary argument. They claim that since Jewish continuity requires women to gestate reproductions of Jewish men, all women are reduced to reproductive units, and that “the focus on reproductive project ha[s] continued … to enable the abuses that come along with it.” That is; all that money focused on replicating themselves had the effect of viewing women as baby making machines and that this characterization of Jewish women accounts for the sexual atrocities perpetrated by Epstein and his cohorts. This is, I think, too large a leap. How is it that the desire for more Jewish babies leads to abuse of women?
Where is the connection between fighting assimilation and having sexual encounters with underage non Jewish girls? Further, how do they explain the wealthy Jews involved with Epstein who have no connection to the Jewish continuity project ?
Why do the authors make this peculiar claim based on so little evidence? My guess is that the authors identify as Jewish, but they do not want to bear any responsibility for the behavior of some other Jews. They establish their innocence and that of most other Jews by sectioning off just a small number of very wealthy Jews and, finding them peculiarly focused on reproduction, claim they are prone to acts of sexual abuse. This makes the Epstein scandal not a Jewish problem, but a narcissistic fault in just a few Jews.
More likely, Epstein and many others operated with a sense of impunity. Some of these people were, as the article points out, enamored with reproducing themselves. The only connection I can see between Jewish continuity and Epstein is that the focus on Judaism might have contributed to the apparent belief among some Jews that non Jews are not important and that mistreatment of them is not a problem.
When I wrote this article, Epstein was alive and well in the hands of MCC. Now we have been informed that Epstein committed suicide, and we have no information on whether he left behind any little Epsteins.
The views expressed in this article are the sole responsibility of the author and do not necessarily reflect those of the Blog!
Subscribe to:
Comments (Atom)













